You're reading the Keybase blog.
There are more posts.
When you're done, you can install Keybase.
Introducing Keybase Chat

FRIENDS!
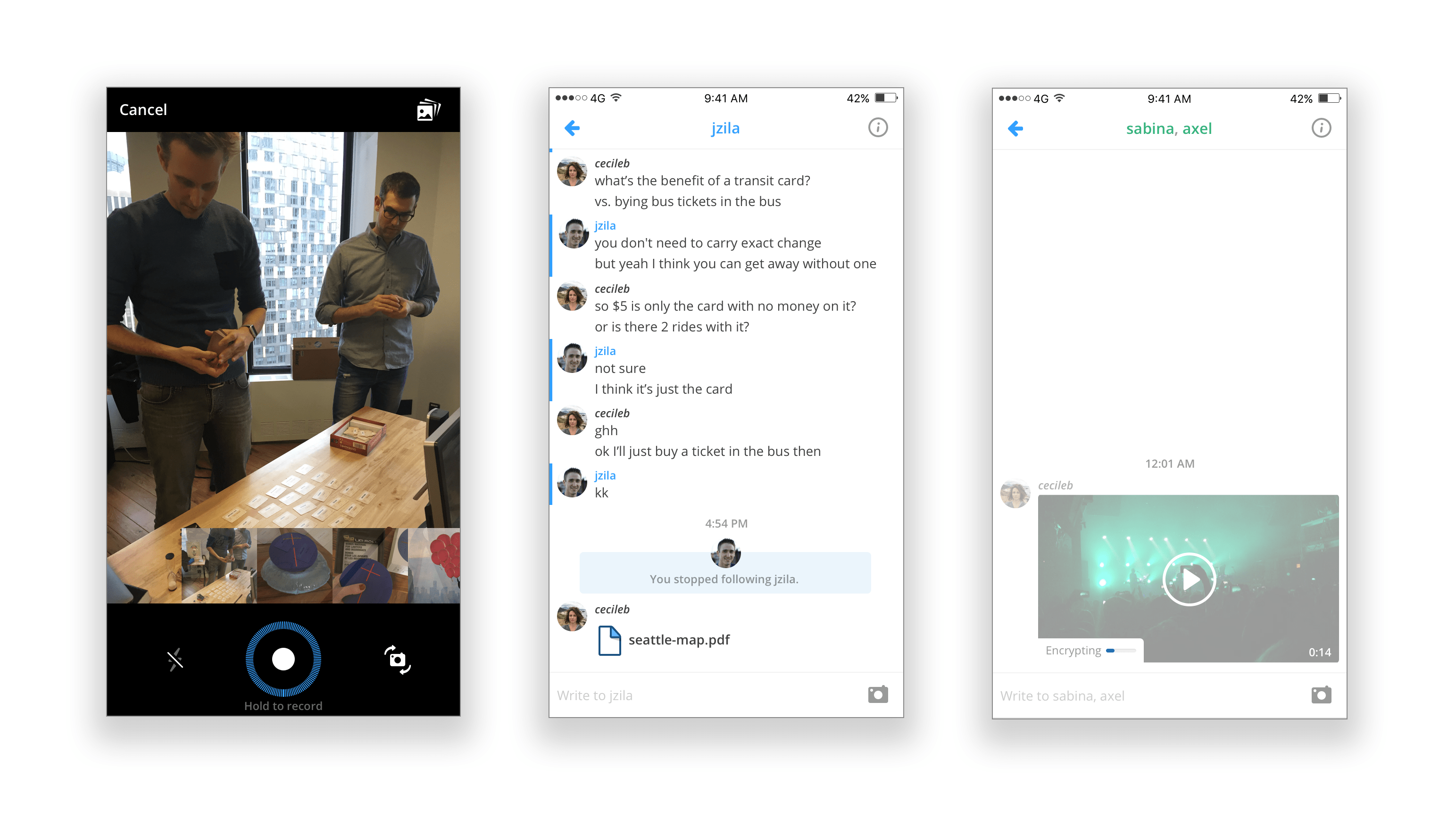
Today we're launching an end-to-end encrypted chat built into Keybase (downloadable here; source code here). It's easier to use than other crypto apps. It's scriptable too.
Screenshot:
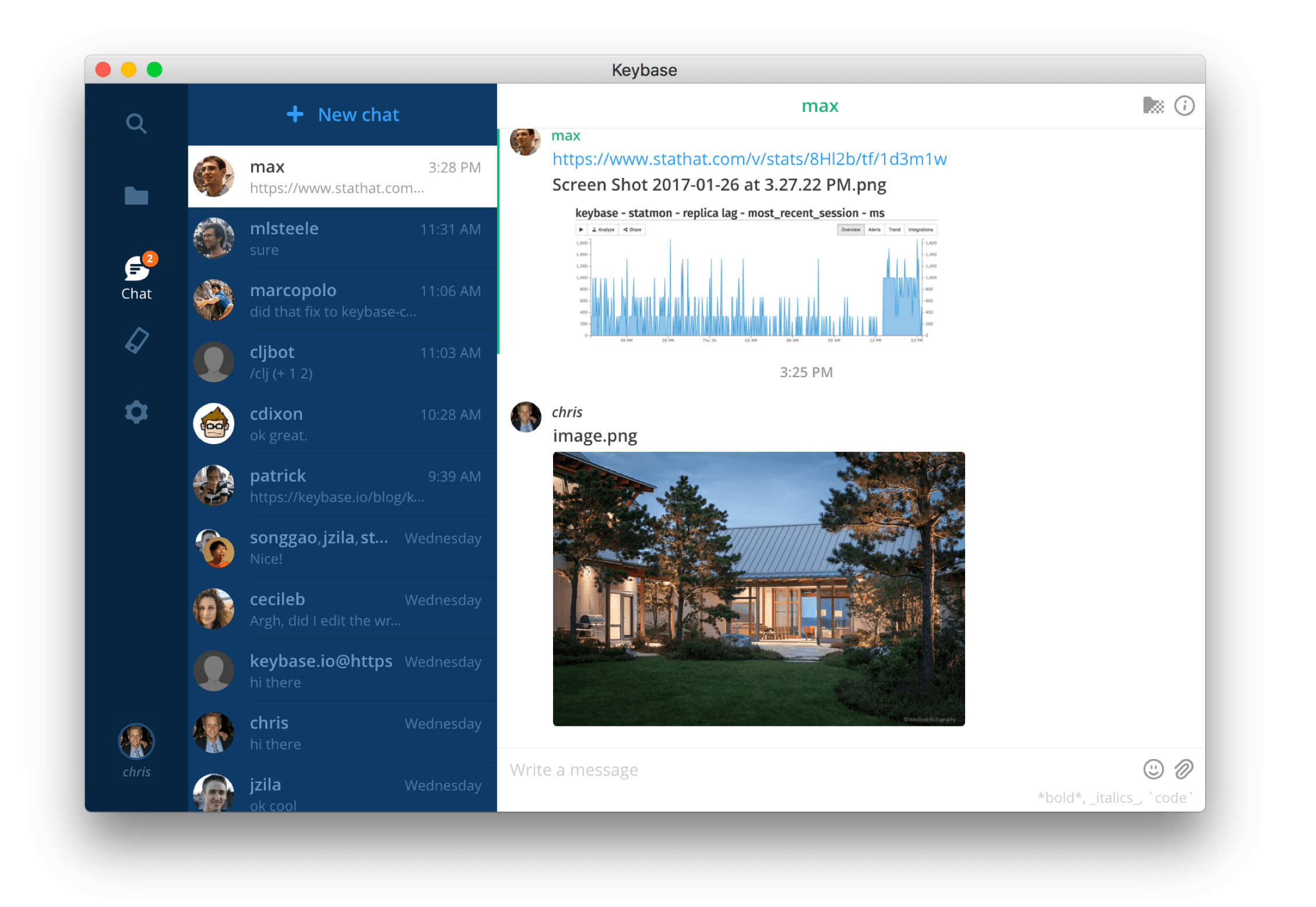
This is way different from other chats, so let's dig in.
It's bigger than your address book
At Keybase we collectively use and love WhatsApp, Signal, and iMessage, to name a few. However, in all those apps: recipients are looked up by phone number or email.
That works ok with friends and coworkers.
But it sucks with people you know on the Internet. First off, they have to give you their phone number in a preliminary back and forth. That takes time and prevents you from sending your message until you hear back.
Then, to make sure you're really secure, you're supposed to compare special codes by meeting in person. That's impossible in most cases.
Keybase is different. For example, in Keybase chat, I can simply use my Hacker News name, malgorithms, as my secure address; no phone number or email needed. My Twitter username would work, too. Or even my Reddit username. So go ahead and message me:
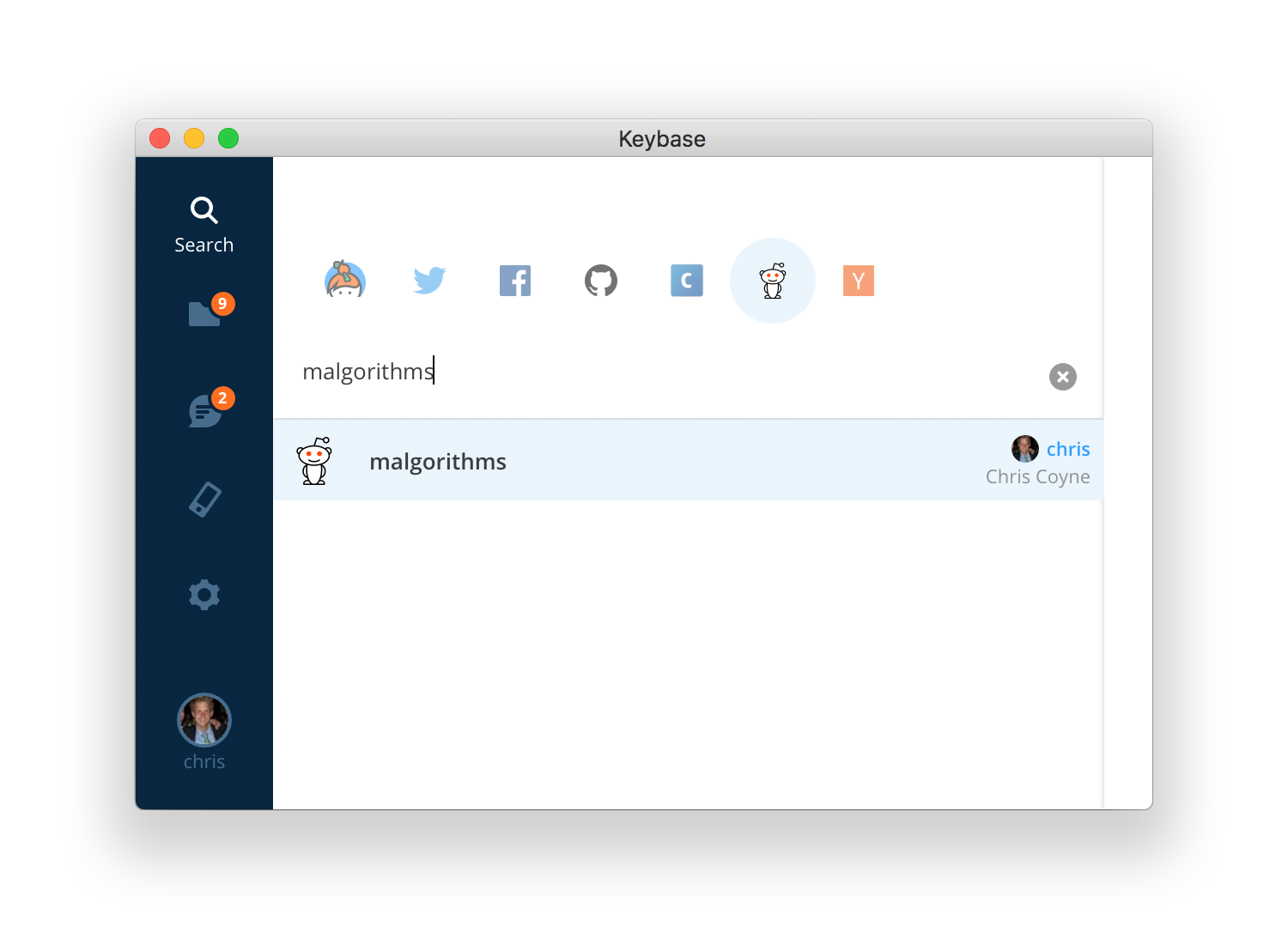
In fact, you could message me using any of my social media aliases, even if I hadn't joined Keybase yet.
How does that work?
If you leave a message for someone on Keybase, and they join later, your computer or phone will rekey the message for them, based on their key posted on Reddit (or whatever service you addressed them by). Since your Keybase app actually checks the proof for you, it's not "TOFU" (trust on first use) like other chats use.
Keybase's mapping between addresses and keys is 2-way verifiable. For example, here's my own Reddit proof. Also, Keybase gives the same answer to everyone. If Reddit.com wanted to be evil and trick you, they would have to trick everyone.
Keybase is just easier. Everyone you know on social media now has an encrypted inbox waiting for them. All without the server ever having a decryption key.
Our goal is end-to-end encryption with minimal friction.
Seeing who you're dealing with
For those who like to think about keys:
Here we see my friend patrick has sent an encrypted message to me using his device, "imac". He picked that name on Oct 9, 2015. Here's the actual key announcement.
Because I follow him, I can think of him as "patrick" -- a single consolidated identity -- instead of the other disparate ways I know him. Following on Keybase means I've signed a summary of who I think "patrick" is:
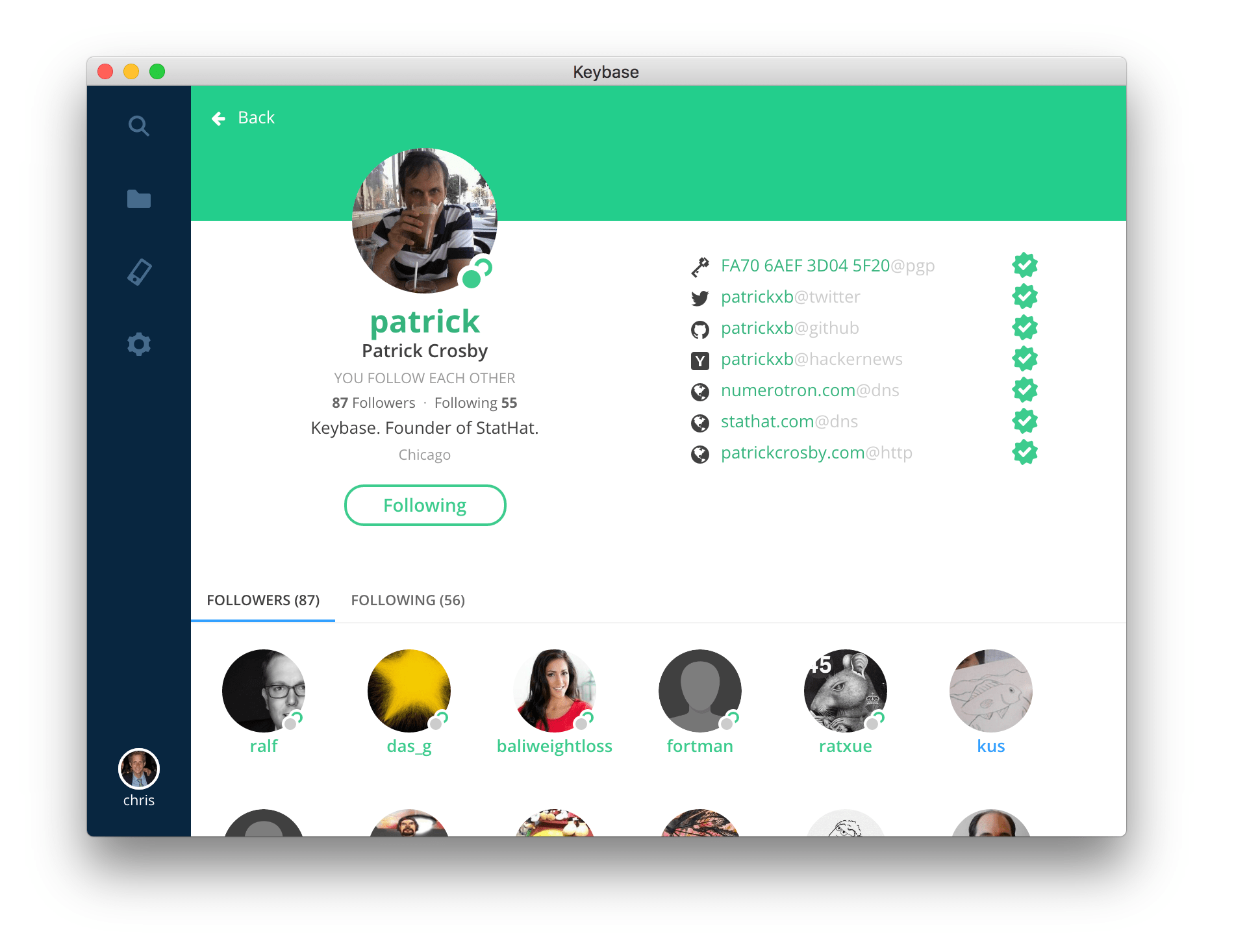
My own Keybase app will continue to check all those assertions as I deal with Patrick.
As for key management, this isn't like PGP mail. Each device generates its own keys, and the private key never, ever, leaves the device.
Your messages actually survive when you upgrade or add devices
Seems obvious!
WhatsApp and others offer Forward Secrecy, which promises that if someone steals your device and extracts your private key from it, they can't decode previously recorded conversations. That is, assuming they didn't also steal the messages from the device, when they stole the key.
This does come at great UX cost, however. Apps with FS on all messages must choose one of these:
COMPROMISE #1: all messages, photos, and videos get lost forever on a device upgrade
COMPROMISE #2: violate Forward Secrecy by letting users back up messages or otherwise transfer them around.
Compromise 2 is flat-out horrible because it violates an implicit social contract. Unless you ask your friends first for permission, then backing up a Forward Secrecy chat is the crypto equivalent of screengrabbing a Snapchat.
Compromise 1 renders a primary chat app unacceptable for many people, but it is the secure, correct answer for any app with FS.
How Keybase solves this problem:
- End-to-end encrypt all messages,
- but only "exploding messages" (coming soon) will have FS.
- Therefore, your history will survive, encrypted, except for the messages you choose.
We feel strongly this is the right answer for most people.
keybase chat works from the command line
Advanced hacker? Make plans straight from your HUD.

Chats support multiple people, and you can pipe from stdin:
keybase chat send chris "Beer Saturday? 🍻"
keybase chat send rick,morty "Blips and Chiiiiiitz"
echo "Sup, Jed" | keybase chat send jedmccaleb@twitter
Most important, there's an API interface, which takes JSON as stdin and pipes JSON to stdout. This is how you'd most likely program the chat API. Feeling creative? Put some program on a server and let it message the crap out of your friends.
Here in the office, we wrote a simple bot that the team can send math questions to.
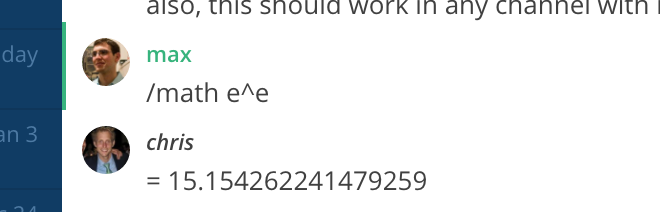
If you’re interested, more API examples are here:
keybase chat help api
You can broadcast --public messages
Finally, there is one message that isn’t encrypted: signed, public broadcasts. This only works from the command line.
# replace `chris` with your username
keybase chat send --public chris "New foo.iso. Hash is 54e5..."
You can read anyone’s broadcast history.
keybase chat read --public chris
[1] [chris 3d] Server restart [reason: mouse feces]...
[2] [chris 7s] New foo.iso. Hash is 54e5...
We're expanding it fast
This first version supports basic text messages up to 4000 chars and attachments. That's it. We'll be adding a bunch more features soon.
And we'll launch our phone app soon. Crypto for everyone.
If you have the latest Keybase installed, please say hi.
:-)
- Try it: https://keybase.io/download
- and send me your feedback: https://keybase.io/chris
FAQ
Does this use PGP?
No. Even if you have a PGP key on your Keybase profile, these messages are only encrypted with your Keybase device + paper keys. People aren't so great at managing and moving PGP private keys around, so PGP keys are not included in our chat or filesystem. You can read more about our key model here.
The basic idea here is that non-technical people won't get confused and do something irresponsible.
You can, however, address someone by their PGP key! I've proven ownership of this PGP key, which your own client will verify:
keybase chat send 94AA3A5BDBD40EA549CABAF9FBC07D6A97016CB3@pgp 'hi whoever owns 9701 6CB3'
You can think of a PGP key as another part of a user's identity, and therefore one of the assertions you can make, like a Twitter address.
What's preventing Keybase from adding a device for me, that's really just owned by Keybase or nefarious shadow organization X?
Key additions must be signed publicly into your signature chain by a currently active key, as determined by your signature chain. This is verified by everyone you chat with.
You'll see this policy in action when you install Keybase on a 2nd computer. It'll make you either (a) type something on your first computer, or (b) enter a paper key. This isn't just two-factor auth with server trust. The old key is signing a statement about the new key, and the new key is countersigning.
If someone were to steal a device of yours that wasn't revoked, they could use it to read your data (of course), and therefore provision another new device. But that would be publicly discoverable because of the new device name announced in your signature chain.
If you lose all of your devices and paper keys, you will lose your data. Keybase cannot read any of your encrypted data. So it's extra important to make sure you have at least 2 devices or paper keys. Maybe even 3, if you start caring about your data in Keybase. When our mobile apps launch, your phone will be a great device for provisioning and chatting.
What block/muting features are available?
This version supports muting individual conversations, so you're not interrupted and can ignore conversations that you're not interested in. More advanced blocking / reporting / nuking features will be available in an upcoming release.
What about metadata?
Like with most chat apps, the Keybase servers will see who you're looking up.
For a given message, Keybase servers know who sent it, approximate size, who the recipients are, and an ID for the channel. All of this is a requirement for performance and (upcoming) mobile notifications.
It's better than PGP because of many modern crypto best practices, easier and safer key management, and easier and safer identity lookups.
If your biggest fear is hiding whom you're talking to, none of the apps mentioned on this page are safe unless you're coming in over Tor, with no info connected to your real identity, in a library or cafe, and wearing a disguise.
What can I do to help?
Play with it, please, and let us know what features you want added.
This is a post on the Keybase blog.
- Keybase joins Zoom
- New Cryptographic Tools on Keybase
- Introducing Keybase bots
- Dealing with Spam on Keybase
- Keybase SSH
- Stellar wallets for all Keybase users
- Keybase ♥'s Mastodon, and how to get your site on Keybase
- Keybase is not softer than TOFU
- Cryptographic coin flipping, now in Keybase
- Keybase exploding messages and forward secrecy
- Keybase is now supported by the Stellar Development Foundation
- New Teams Features
- Keybase launches encrypted git
- Introducing Keybase Teams
- Abrupt Termination of Coinbase Support
- Keybase chooses Zcash
- Keybase Filesystem Documents
- Keybase's New Key Model
- Keybase raises $10.8M
- The Horror of a 'Secure Golden Key'
- Error Handling in JavaScript