You're reading the Keybase blog.
There are more posts.
When you're done, you can install Keybase.
NEWS FLASH: Keybase Exploding Messages
Hi everyone. Starting today, you can put a short fuse on your Keybase chat messages. This works for 1-on-1 chats and also inside team, group, and community channels.
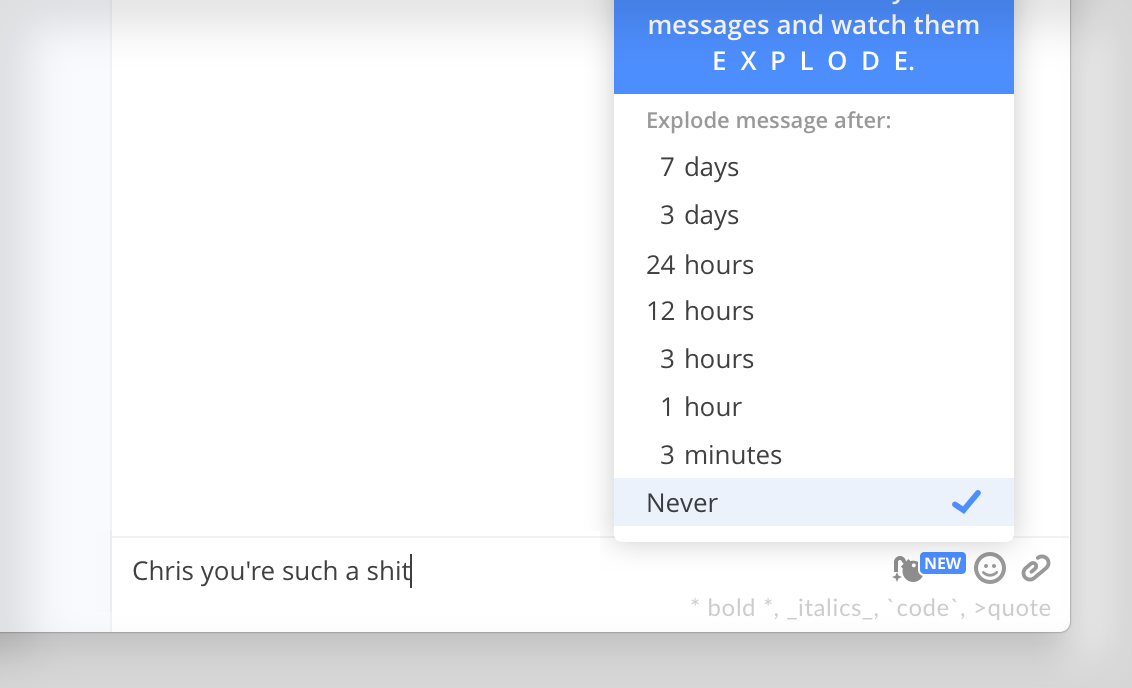
demonstration from my brother
We recommend your most intimate and most corporate messages get the exploding treatment. Each end of the professionalism spectrum. Don't put that dank meme or Income Statement in plaintext, people. Put it in Keybase, so it's encrypted.
And if you'd like it to be temporary, make it explode.
Some details:
They blow up
When the time comes, KA-BOOM

When the countdown hits zero, everyone throws away the plaintext and ciphertext.
Exploding messages have forward secrecy
Forward secrecy means your apps use temporary "ephemeral" keys that are thrown away.
To be clear, all Keybase messages - not just exploding ones - are end-to-end encrypted. No one can read them without compromising one of your devices.
Forward secrecy is something extra. It protects you if someone in the future steals your device's key and also has access to old recorded messages, say by scooping up ciphertexts as a man-in-the-middle.
Forward secrecy works extra well with timed messages because your device destroys both the decryption keys and plaintext.
Splosions from the command line
You can also send exploding messages from your terminal of choice.*
# example: messaging a friend
keybase chat send --exploding-lifetime "30s" friend1234 \
"Yo - meet @ 10pm under the powerlines. Bring the stuff"
# example: corporate excellence
keybase chat send --exploding-lifetime "6h" acmecorp.finance \
"That is NO laughing matter, James."
If you're writing a bot, you can pipe JSON to keybase chat api. Example:
{
"method":"send",
"params":{
"options":{
"channel":{
"name":"vegetarians.bots"
},
"exploding_lifetime":"1d",
"message":{
"body":"smellbot has detected meat in the office foyer."
}
}
}
}
You can get more API examples with keybase chat api --help.
That's it!
Another step forward for Keybase. Cryptography for everyone.
More stuff soon,
💖 Keybase
FAQ
Are there docs on how this works?
Yes, here are the crypto docs. And here's the Keybase source code.
My team uses Telegram and I'm scared shitless.
Hugs
What's the point, if someone can just take a screenshot?
I answered this on Hacker News.
Why don't all messages have forward secrecy?
We've blogged about this before. It's not the right answer for a mainstream chat replacement, because it forces dangerous behavior and/or makes you lose all your group's messages when you update devices.
Still, it's up to you! Now you can have all the forward secrecy you want with Keybase.
What about repudiation?
Repudiation is launching in ~3 weeks.
So yes, in chats up to 100 people, messages will be pairwise MAC'ed. Pairwise MAC'ing doesn't scale for mega-large community chats, so those messages are still signed & encrypted in the traditional sense. This seems like the best balance.
Some have argued repudiation is a silly feature. After all, who, in the history of humanity, has ever not gotten in trouble for something that leaked, just because it wasn't cryptographically signed?
Anyway, this is minimal overhead with some benefit, so we're doing it.
Does the timer begin when the message is sent or received?
Sent.
This seems like the only sensible answer for group chats. And we can't have a different answer for 1-on-1 chats and group chats. That would confuse people. Not the kind of person who reads an FAQ such as yourself, of course.
So our answer is simple: you set a timer and the message is gone after that time.
I have nothing to hide
Because no one is trying to hurt you
This is a post on the Keybase blog.
- Keybase joins Zoom
- New Cryptographic Tools on Keybase
- Introducing Keybase bots
- Dealing with Spam on Keybase
- Keybase SSH
- Stellar wallets for all Keybase users
- Keybase ♥'s Mastodon, and how to get your site on Keybase
- Keybase is not softer than TOFU
- Cryptographic coin flipping, now in Keybase
- Keybase is now supported by the Stellar Development Foundation
- New Teams Features
- Keybase launches encrypted git
- Introducing Keybase Teams
- Abrupt Termination of Coinbase Support
- Introducing Keybase Chat
- Keybase chooses Zcash
- Keybase Filesystem Documents
- Keybase's New Key Model
- Keybase raises $10.8M
- The Horror of a 'Secure Golden Key'
- Error Handling in JavaScript