A place for work (or not)
We use public key cryptography to ensure your messages stay private. Even we can’t read your chats.
We use public key cryptography to ensure your messages stay private. Even we can’t read your chats.
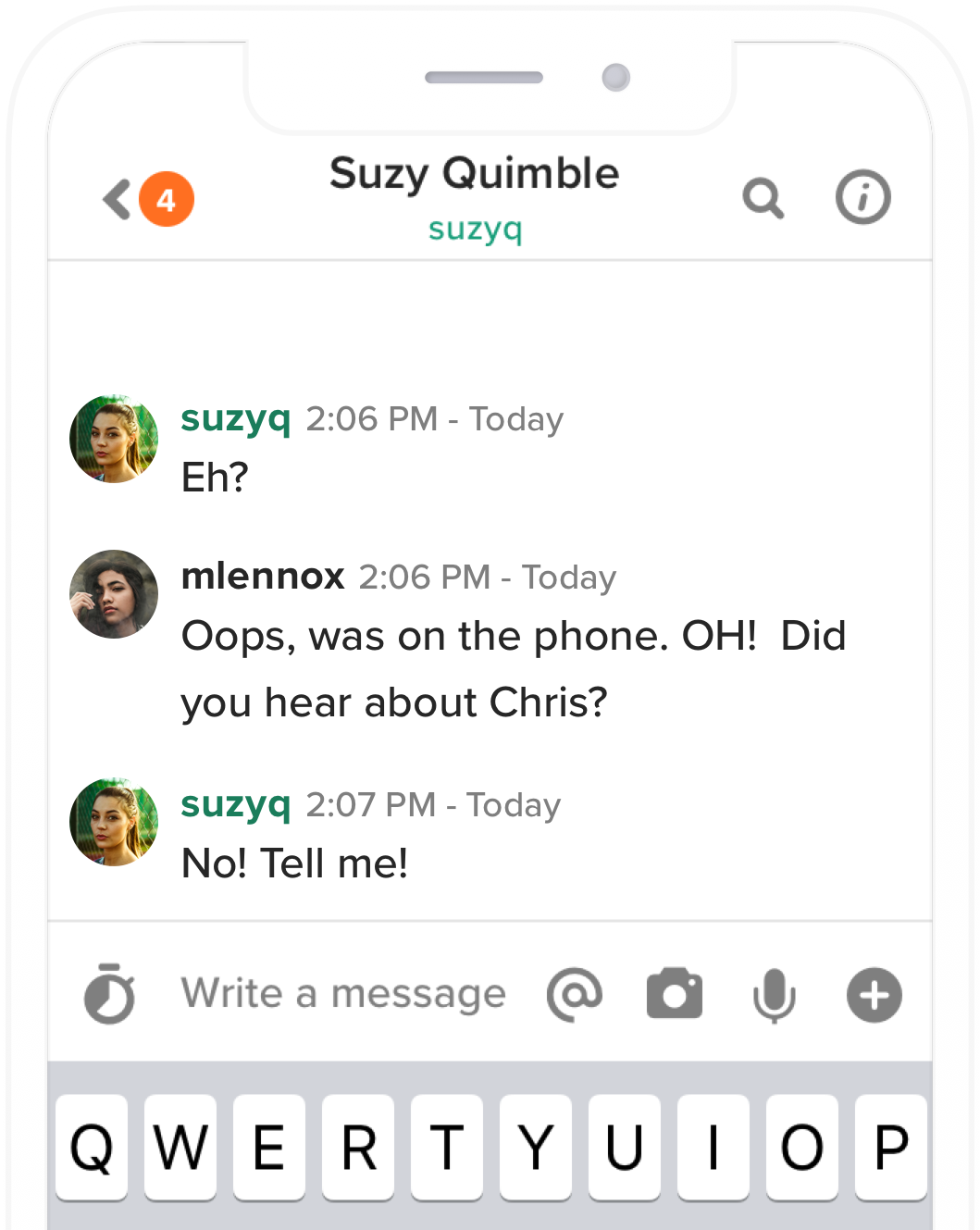
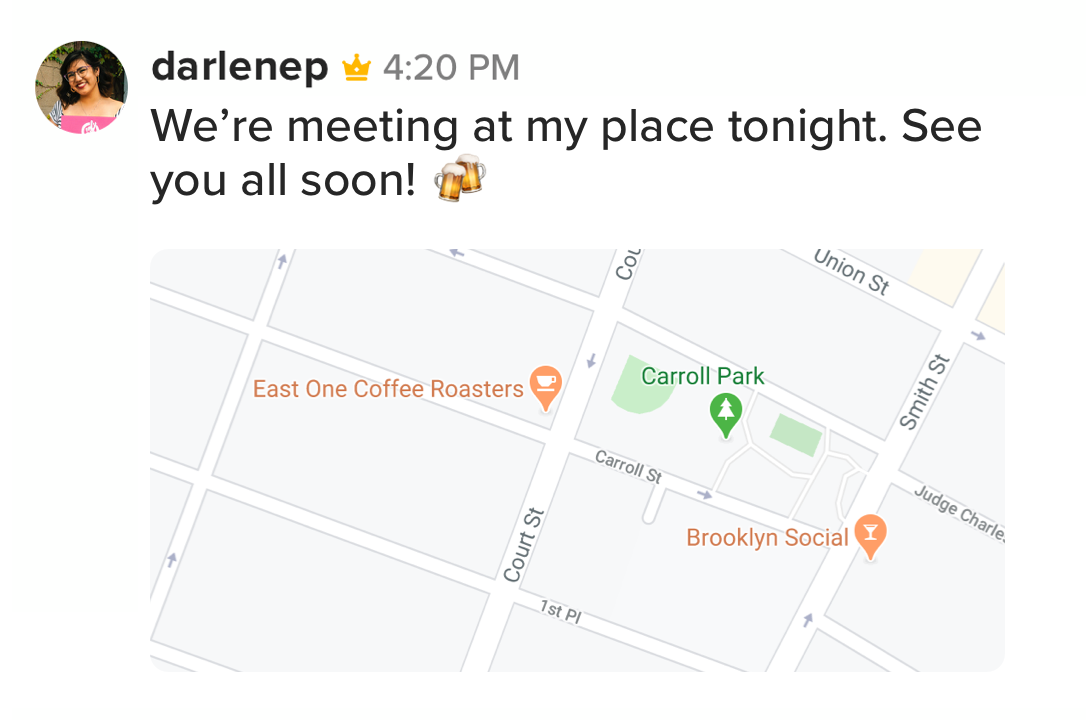
Keybase works for families, roommates, clubs, and groups of friends, too.

Keybase connects to public identities, too. You can connect with communities from Twitter, Reddit, and elsewhere.



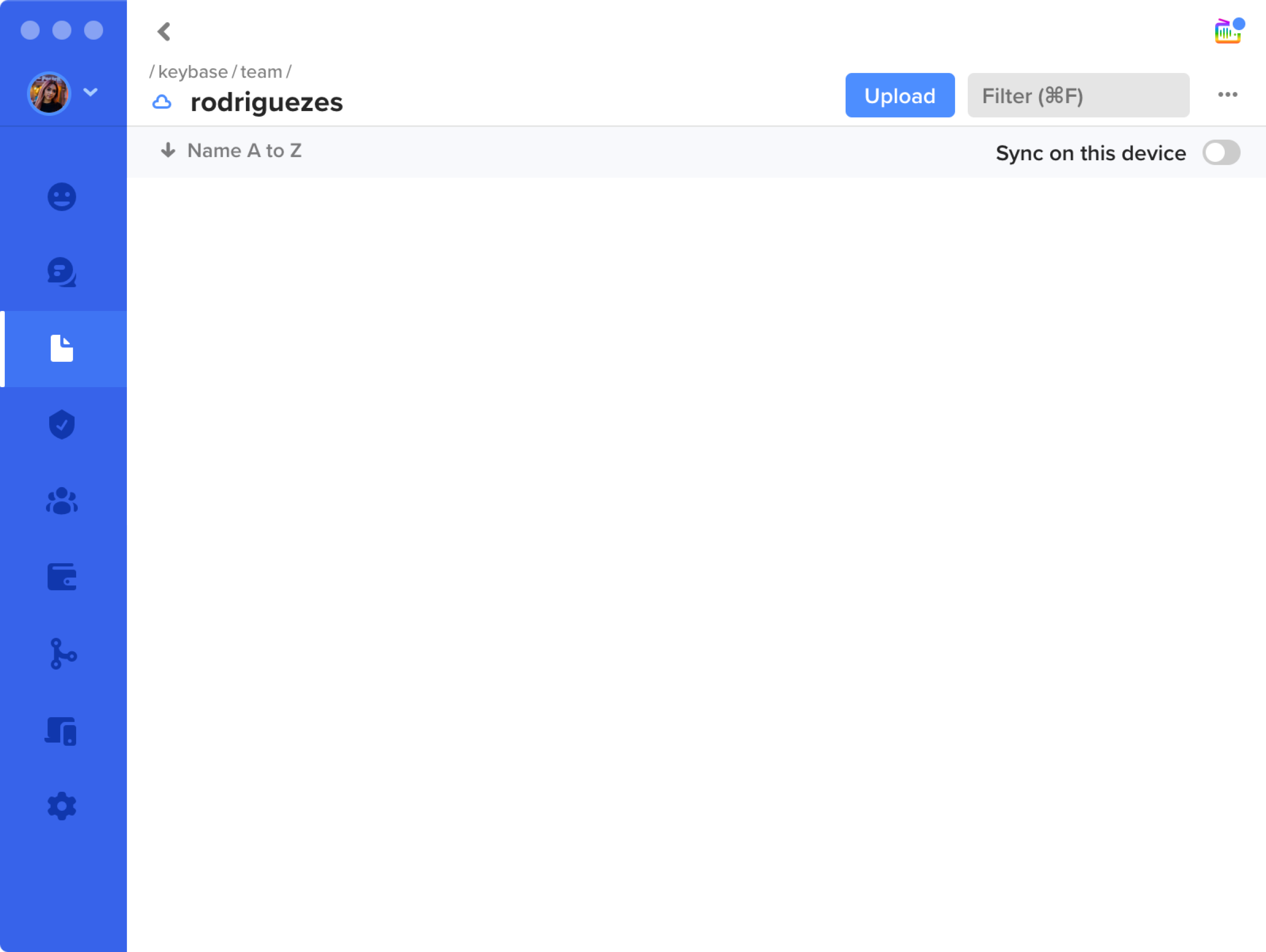
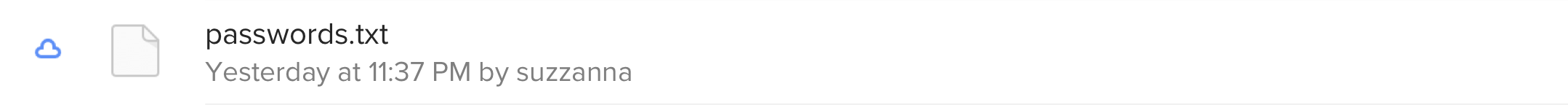
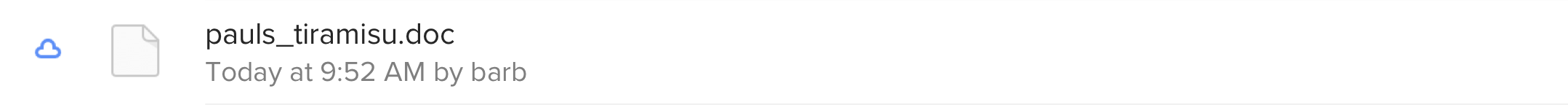
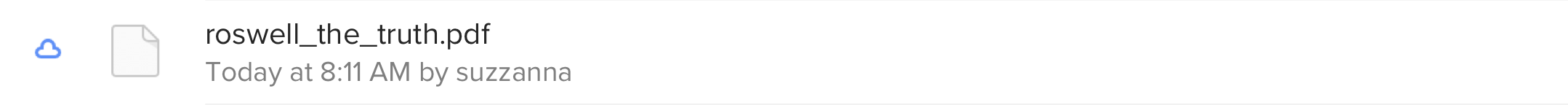
Don’t live dangerously when it comes to documents. Keybase can store your group’s photos, videos, and documents with end-to-end encryption.