You're reading the Keybase blog.
There are more posts.
When you're done, you can install Keybase.
🚀 Keybase launches encrypted git
Every now and then you want to make a repository that's private. Not for an open source project, but for other stuff: research, writing a novel, family history, or a community's private files. Or your team's API keys, devops secrets, and business docs.
What do you do?
A free, happy solution
Starting today in the Keybase app, you'll see a new Git tab. From there, you can make hosted repositories. Just type a name and you're good to go. From zero to clone, it's less than 60 seconds.
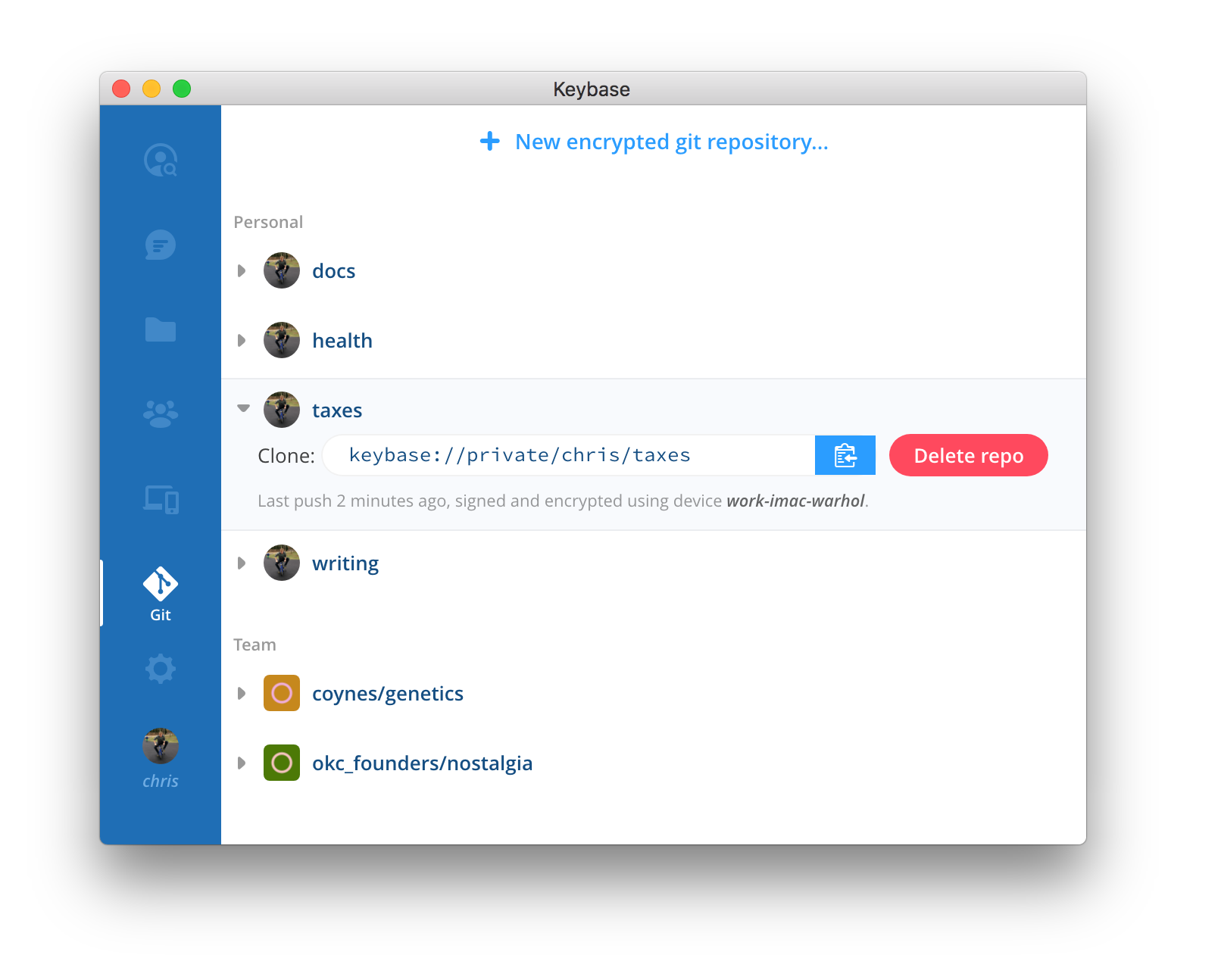
Above, you can see I've made personal repos: docs, health, taxes, and writing. I check them out on all my computers.
I also have access to team repositories made by my friends, family, and coworkers: founding docs for Keybase; some nostalgia from the old OkCupid and SparkNotes days; maybe even some shared erotic art that's Not Safe For Work.
This is working today and you, too, can use it.
Actually private
It is end-to-end encrypted. It's hosted, like, say, GitHub, but only you (and teammates) can decrypt any of it. To Keybase, all is but a garbled mess. To you, it's a regular checkout with no extra steps.
Even your repository names and branch names are encrypted, and thus unreadable by Keybase staff or infiltrators.
We think this is better than paying a fee to store it in plaintext. Remember, it is impossible to delete cloud data with any kind of confidence, and your host may already be compromised.
Underneath the hood
Git supports remote helpers. And we've made an open source one.
You'll see a clone address like this:
git clone keybase://private/chris/docs.git
Keybase's remote helper performs all the crypto while letting git do its thing. This might sound impressive, but Keybase has not reimplemented git from scratch. We provide a remote helper, powered by the excellent go-git project, which we've begun contributing to.
We bring to the table: (1) crypto, (2) team + multi-device key management, (3) a safer concept of identity. This is stuff we've already built, so this project was 99% done when we started. A rare treat in crypto.
Authenticity
Everything is signed.
All data you push is signed by your device's private key, which never leaves your device. Fetches are cryptographically verified or else they'll fail. Unlike casual PGP signing of commits, which no one in the world ever does, this is fully enforced for yourself or team.
You don't need to think about it: if you do a git pull, you'll only get the data if it's bit-for-bit exactly what the pusher pushed.
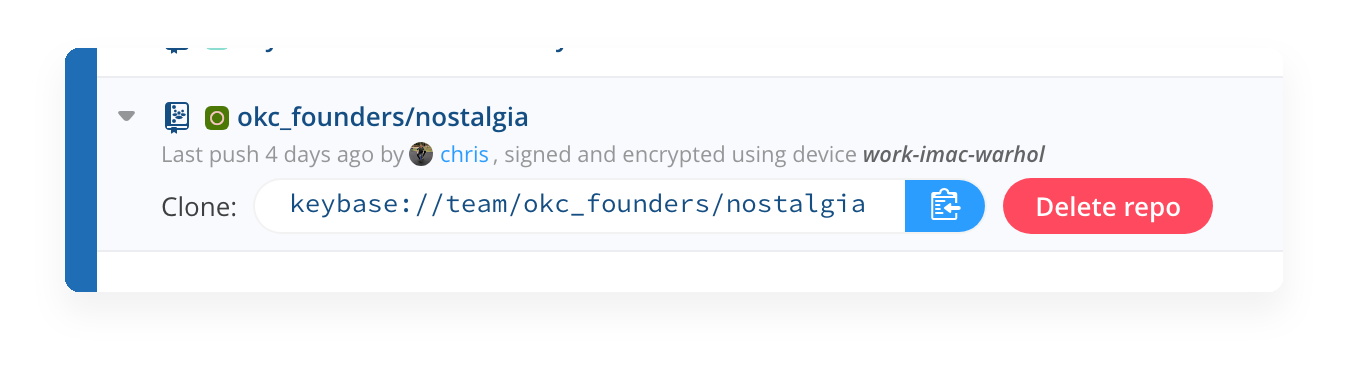
Above we see I used work-imac-warhol,
a device I provisioned 2 years ago.
What's it missing?
Well, there's no website interface. No pull requests, no wiki, no issue tracking. It's git, pure and simple. But it's actually encrypted and super easy to use.
It works with GitHub Desktop.
Prefer a Git visual interface? No problem:
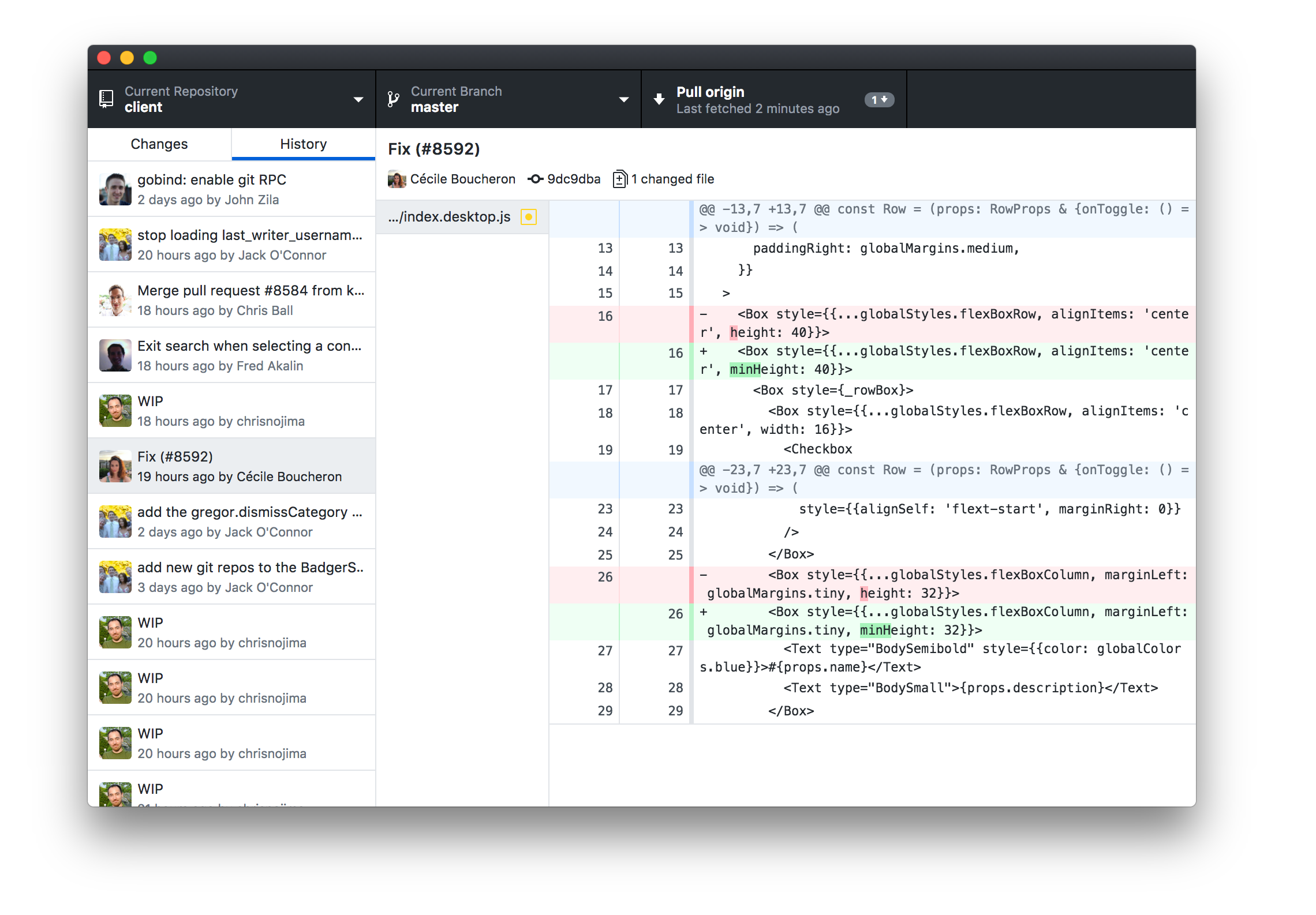
Just drag your local clone onto the app.
Moving an existing repo to Keybase
If you already have a "private" repository hosted in Bitbucket, Gitlab, GitHub, or wherever, you can move it to Keybase. For git novices, here's a wizard that pulls your branches too:
That's all!
And as a final reminder, Keybase comes with encrypted chat, so your team can discuss your commits with ease.
~/ >keybase chat send beliebers "praise be crypto"
Cheers, because we wanted to make this for a while.
❤️ Keybase
~ Anticipated q's ~
Wait, what's this about teams?
YES! Keybase has been working on cryptographically-defined teams for many person-years.
Metadata?
Keybase's servers know who's on your team, who's pushing and fetching, and which devices are being used. Keybase recognizes distinct repositories (for example, it has unique id's for every repo), but it doesn't know what you've named your repositories, your branch names, or any contents.
What are the limits?
Very high, because sometimes you have to make a product that's better on every axis. It's a dream project for us.
You can have as many repositories as you want, but the total for your personal repositories can't exceed 100GB. Each team also gets 100GB.
What if my computer is compromised?
Your work is only as safe as your endpoints, so we can't help you there.
What if we're living in a simulation?
Keybase offers no guarantees against sophisticated side-channel attacks by higher-level entities.
Why not just make a bare repo in KBFS?
The Keybase filesystem journals changes and syncs them after writes, kind of like Dropbox. Which means you and another team member could be fighting each other and make a conflicted HEAD, where there'd be 2 copies side by side. Similarly, you shouldn't put git repos in Dropbox.
Keybase's git prevents this by locking.
Also: it's nicer to use the Keybase app to discover and manage your teams' repositories.
What about public repositories?
This is not exposed in the GUI but it can work. Perhaps more news on this soon.
So is this signing my commits?
No, this is happening at a lower level, (1) to allow encryption, and (2) to ensure no unsigned or unencrypted data makes it in. Intuitively you can think of it as you and your teammates using a cryptographic secure storage layer for your git origin that doesn't really understand git.
Your commits themselves are untouched from git's perspective, so if you mirror your repository elsewhere, it'll be a regular checkout.
What if I hate it/you?
:-(
Don't you know I could just do X instead? Crypto is so easy bleah bleah bleah
Ok!
What can I do to help?
Play with it, please! Or you could always contribute. We accept PR's. And we are hiring.
This is a post on the Keybase blog.
- Keybase joins Zoom
- New Cryptographic Tools on Keybase
- Introducing Keybase bots
- Dealing with Spam on Keybase
- Keybase SSH
- Stellar wallets for all Keybase users
- Keybase ♥'s Mastodon, and how to get your site on Keybase
- Keybase is not softer than TOFU
- Cryptographic coin flipping, now in Keybase
- Keybase exploding messages and forward secrecy
- Keybase is now supported by the Stellar Development Foundation
- New Teams Features
- Introducing Keybase Teams
- Abrupt Termination of Coinbase Support
- Introducing Keybase Chat
- Keybase chooses Zcash
- Keybase Filesystem Documents
- Keybase's New Key Model
- Keybase raises $10.8M
- The Horror of a 'Secure Golden Key'
- Error Handling in JavaScript
